Summary
Like sprinkler systems that stop fires, Ransomware Containment stops active ransomware outbreaks.
Read time: 4 minutes
Ransomware and an office fire are a lot alike. And protecting against a ransomware attack is a lot like fire-proofing your office.
To prevent a fire, you have fire doors and fire-proof floors in production areas. To keep arsonists out, access is only granted via keycard. You might even have cameras watching entrances. Fire extinguishers are everywhere.
You also have smoke detectors everywhere. But with all the fire-proofing measures, why do you need smoke detectors? Because we know that all of the above measures don’t work 100% of the time.
So, you put smoke detectors in your building to notify everyone when a fire is starting.
But a smoke detector can’t stop a fire. So, your building has a sprinkler system to account for this potential need. You hope it will never activate, but it is there to cope with the worst-case scenario.
How ransomware prevention security is like fire prevention measures
Endpoint and server security measures work much like fire prevention.
Anti-spam email monitoring and endpoint protection for workstations and servers act like fire doors, keycards, and smoke detectors. Their purpose is to prevent a security event from happening. Should malware get in, most of these solutions will alert you (like a smoke detector) of the situation. In most cases, these measures prevent a security event.
But what happens if an attack unfolds and encryption begins?
The missing element in ransomware prevention
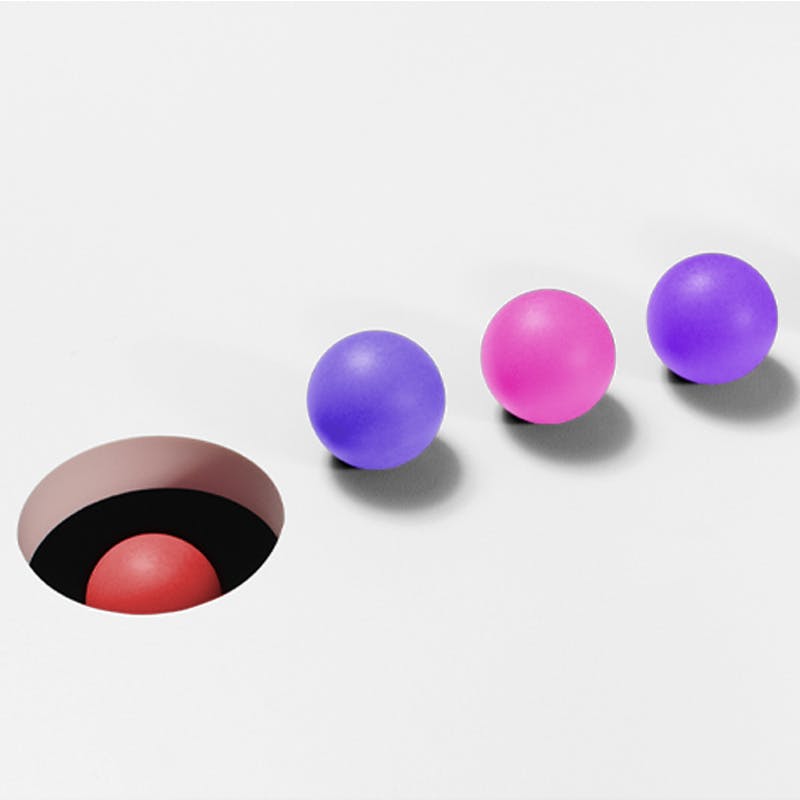
Ransomware protection measures have typically lacked the “sprinkler system” to put out the fire. What would this sprinkler look like? It would stop the ongoing encryption from escaping the PC or device and locking up files across the business.
Today that has changed. The “sprinkler system” now exists. It’s called Bullwall Ransomware Containment.
Is Ransomware Containment the answer for you?
Ransomware Containment does not replace your current security solutions, policies, and protections. It complements them, providing an additional critical layer of protection missing today.
Its purpose is to act like that “sprinkler” to put out the worst-case scenario of a ransomware outbreak. Ransomware can encrypt 10,000 files per minute per device.
If five endpoints were compromised, you could lose 50,000 files each minute.
Isolation limits the impact to one device or file share. And that’s why the containment offered by Ransomware Containment addresses the question that keeps many business leaders, IT professionals, and security executives awake at night:
What can we do if a ransomware outbreak occurs?
With Ransomware Containment, you know the answer. The infected device will be isolated, and the impact on your business dramatically reduced.
To see more details of how it works, check out our Ransomware Containment services page.
For a detailed summary of the software, you can visit our Ransomware Containment software page.
Read more about ransomware and how to protect your business in the ebook “Ransomware, Containment, and Isolation."
- 1. https://assets.sophos.com/X24WTUEQ/at/4zpw59pnkpxxnhfhgj9bxgj9/sophos-state-of-ransomware-2022-wp.pdf
Recommended for you
 Case Studies
Case StudiesDigital transformation for schools saves the day
California school district invests in cybersecurity and automates processes to drive efficiency.
 Webinars
WebinarsWebinar: Containing Ransomware Outbreaks
Learn about the new strategy Infosec leaders are using to stop ransomware outbreaks and protect their organizations against ransomware attacks.
 Webinars
WebinarsWebinar: Protect with ransomware containment
Ransomware can encrypt more than 50,000 files per minute. In this webinar, our experts share how to prevent an active attack from devastating your business.
- 1. https://assets.sophos.com/X24WTUEQ/at/4zpw59pnkpxxnhfhgj9bxgj9/sophos-state-of-ransomware-2022-wp.pdf

